ISO 27001 Explained Simply: What It Is, Why It Matters, and Who Needs It
A beginner-friendly guide to ISO 27001 for startups and decision-makers. Learn what ISO 27001 is, why it matters, and whether your business needs certification.
Welcome to Your Resource for Cybersecurity Insights and Education for a Safer Digital World.
This cybersecurity blog, Isosecu, is dedicated to empowering individuals and organizations with essential knowledge to navigate the complex digital landscape safely. Our mission is to provide comprehensive cybersecurity education, raising crucial awareness about emerging threats and effective defenses. Through insightful articles, practical guidance, and in-depth analyses, we aim to foster responsible digital citizenship, ensuring our readers are well-equipped to protect their online presence and contribute to a more secure internet.
A beginner-friendly guide to ISO 27001 for startups and decision-makers. Learn what ISO 27001 is, why it matters, and whether your business needs certification.

Master cybersecurity risk identification in 2026. Learn how every role from the C-Suite to HR contributes to a resilient enterprise security posture.
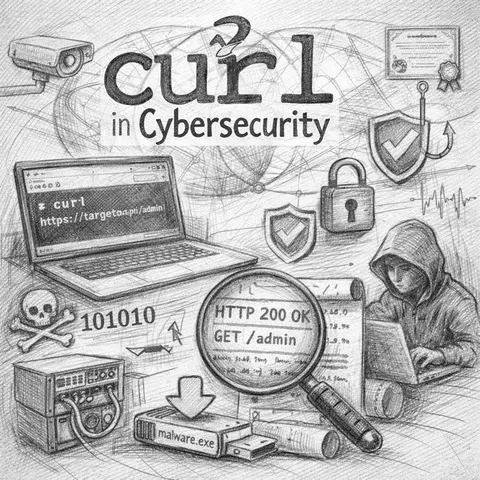
Learn how the curl command is used in cybersecurity for API testing, threat hunting, incident response, malware analysis, and secure data transfer.
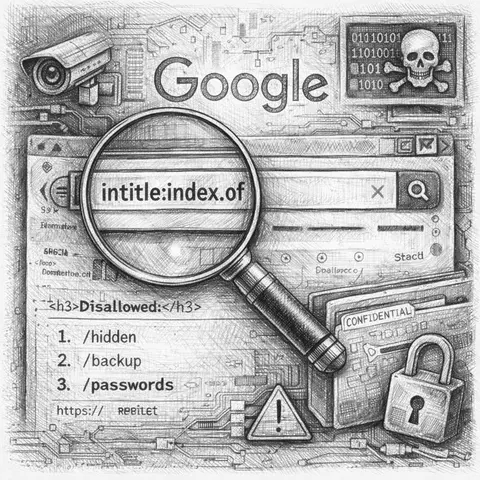
An exploration of Google Hacking history, advanced search operators, and practical examples for security professionals.
An in-depth guide to the Nikto web vulnerability scanner—how it works, what it detects, limitations, and how security teams can use it responsibly.
Can You Be Tracked Through JavaScript?
Don't Click! The Essential Guide to Spotting Phishing and Scams
Double Your Defense with Multi-Factor Authentication (MFA/2FA)
Stay Safe and Secure - The Power of Software Updates
One Domain, Many Faces: How Geolocation Shapes Online Content
Ransomware Preparedness and Response
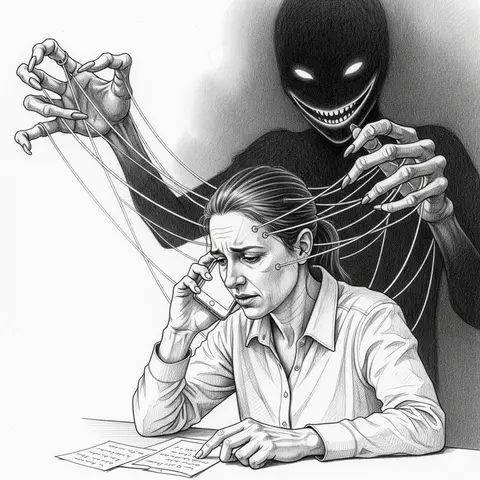
Understanding Scam Calls - Psychological Tricks and How to Protect Yourself
Hardening Developer Workstations: Your First Line of Defense
Check our Blog for more articles.