 Linux
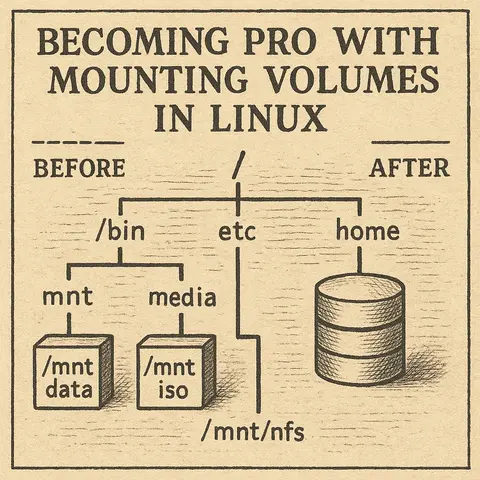
LinuxBecoming Pro with Mounting Volumes in Linux
A complete guide to mounting volumes in Linux, starting from the basics and progressing to advanced scenarios with practical examples.
Sep 22, 2025Cybersecurity
The Microsoft Windows operating system, at its core, relies on two fundamental components for its operation, configuration, and data management: the folder structure and the Registry. Understanding these internals is crucial for anyone managing a Windows system, from everyday users to cybersecurity professionals, as they directly impact system stability, application functionality, and overall security.
The Windows file system is organized in a hierarchical, tree-like structure, starting from the root of each drive (typically C:\). This organization helps manage billions of files and folders efficiently, making it easier for both users and applications to store, access, and retrieve data.
Let's explore some of the most critical directories and their significance:
C:\Windows: This is the heart of the Windows operating system, containing core system files, drivers, and various utilities essential for Windows to function.
C:\Windows\System32: A critical subfolder within C:\Windows. Despite its name, on 64-bit Windows versions, it contains essential 64-bit system files, executables (like cmd.exe, powershell.exe), and dynamic link libraries (DLLs). It's a frequent target for malware that attempts to replace or modify legitimate files, or inject malicious DLLs for persistence.C:\Windows\SysWOW64: (System Windows on Windows 64-bit) On 64-bit Windows, this directory holds 32-bit system files and DLLs. It ensures compatibility for 32-bit applications running on a 64-bit OS. Attackers might target this directory to leverage 32-bit vulnerabilities or hide malicious 32-bit components.C:\Windows\Temp: A temporary directory used by Windows and various applications to store temporary files. Malware often uses this folder during its execution phase to drop initial payloads or temporary components.C:\Program Files (and C:\Program Files (x86)): These folders are the default installation locations for most software applications. Program Files typically houses 64-bit applications, while Program Files (x86) is for 32-bit applications on a 64-bit system.
C:\Users: This directory contains individual user profiles for every user account on the system. Each user has a dedicated folder (e.g., C:\Users\YourUsername).
Desktop, Documents, Downloads, Pictures, Videos: Standard folders for storing personal files. These are prime targets for ransomware, which encrypts user data, and for data exfiltration by attackers.AppData: A hidden folder containing application-specific data, settings, and temporary files unique to each user. It's further divided into:
Roaming: Data here roams with the user if they log into different computers in a networked environment (e.g., domain profiles). Malware often uses this location for persistence, as it automatically runs when the user logs in.Local: Data specific to the local machine.LocalLow: Similar to Local, but for applications running with lower integrity levels (e.g., web browsers in protected mode).AppData is a common hiding spot for malware, as it's hidden by default and often overlooked by casual users. Ransomware typically targets files in Documents, Pictures, and Desktop. Strong user permissions (NTFS permissions) are crucial to prevent unauthorized access to other users' profiles.C:\ProgramData: A hidden folder that stores application data that is not specific to a single user. It's often used by applications that run as services or need to share data among all users.C:\Temp: Generally refers to C:\Windows\Temp or C:\Users\<Username>\AppData\Local\Temp. These locations are used by various programs for temporary files. Malware may drop temporary executables here.C:\Windows\System32\config: This directory contains the actual files that make up the Windows Registry hives (e.g., SAM, SECURITY, SYSTEM, SOFTWARE). These are critical for system operation and security.C:\Windows\System32\drivers\etc: Contains the hosts file, which maps hostnames to IP addresses. Attackers often modify this file to redirect users to malicious websites or block access to security updates.C:\Windows or C:\Program Files.System32, config, drivers\etc) for unauthorized changes.C:\Users) and system state to recover from ransomware attacks or system failures.The Windows Registry is a hierarchical database that stores low-level settings for the operating system, installed applications, hardware devices, and user preferences. It's a critical component because Windows constantly refers to it during operation.
The Registry is organized in a tree-like structure, similar to a file system, consisting of hives, keys, and values.
C:\Windows\System32\config and user profile directories). They represent major functional areas of the system.When you open the Registry Editor (regedit.exe), you'll see five root keys (or hives):
HKEY_CLASSES_ROOT (HKCR): Contains information about registered applications, file associations, and OLE (Object Linking and Embedding) object classes. When you double-click a .docx file, HKCR tells Windows which program (Word) should open it.HKEY_CURRENT_USER (HKCU): Stores configuration settings and preferences for the currently logged-on user. This includes desktop settings, user-specific software preferences, and network connections.
HKCU because they don't require administrative privileges to modify.HKEY_LOCAL_MACHINE (HKLM): Contains settings specific to the computer, independent of the logged-on user. This includes hardware configuration, installed software settings, and operating system settings. These settings apply to all users on the machine.
HKLM is a prime target for malware seeking system-wide persistence or to disable security features, as it affects all users. Modifying keys here usually requires administrative privileges.HKEY_USERS (HKU): Contains individual user profile hives for all users who have loaded their profiles on the machine. HKCU is a sub-tree of HKU that corresponds to the currently logged-in user's profile.HKEY_CURRENT_CONFIG (HKCC): Contains information about the current hardware profile used by the local computer. This is essentially a pointer to a specific part of HKLM\SYSTEM.The Registry is a frequent target and tool for malicious actors due to its central role in system configuration and execution.
HKCU\Software\Microsoft\Windows\CurrentVersion\RunHKLM\Software\Microsoft\Windows\CurrentVersion\RunRunOnce, RunServices, etc.# Conceptual example: Adding a malicious entry to the Run key
# This command is for illustrative purposes only and should not be run on a live system without understanding its implications.
# reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "MyMalware" /t REG_SZ /d "C:\Users\Public\malware.exe" /fregedit.exe with extreme caution.HKLM Registry keys, thus limiting the impact of certain malware.The Windows folder structure and the Registry are foundational elements that dictate how the operating system and applications behave. While they enable immense flexibility and functionality, their complexity also presents opportunities for misuse. A thorough understanding of these internals, coupled with diligent security practices, is essential for maintaining the health, stability, and security of any Windows environment.
Security specialists absolutely need an in-depth understanding of the Windows folder structure and the Registry because these are the foundational components that govern how the operating system and applications function, and, critically, how they can be exploited or secured. Malicious software, for instance, frequently leverages specific hidden folders like AppData or modifies critical system directories like System32 for persistence, to hide its presence, or to replace legitimate executables. Similarly, the Windows Registry is a prime target for malware to establish persistence (e.g., by adding entries to "Run" keys), disable security features (like Windows Defender or UAC), or to gather system information for reconnaissance. Without this granular knowledge, security professionals would struggle to effectively detect and analyze malware behavior, conduct thorough forensic investigations, identify misconfigurations that lead to vulnerabilities, and implement robust hardening measures to protect systems from compromise.
Love it? Share this article: