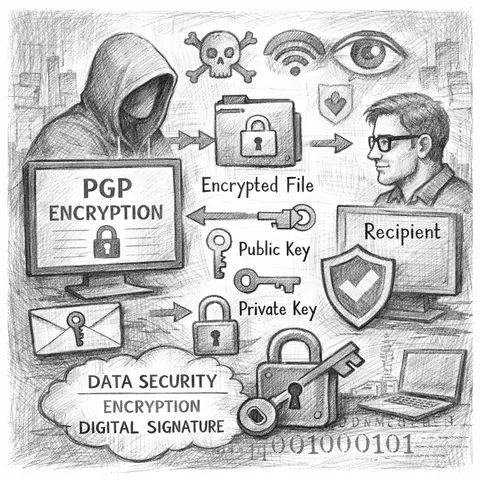
PGP Encryption Explained: Why It Still Matters in Modern Cybersecurity
A deep dive into PGP encryption, its cryptographic foundations, real-world applications, and why it remains relevant for cybersecurity teams today.
Explore the world of cybersecurity with in-depth articles and guides. From ethical hacking to threat defense, master the skills to protect digital assets.
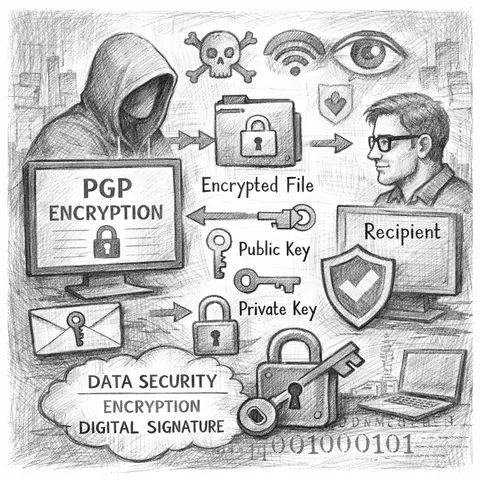
A deep dive into PGP encryption, its cryptographic foundations, real-world applications, and why it remains relevant for cybersecurity teams today.
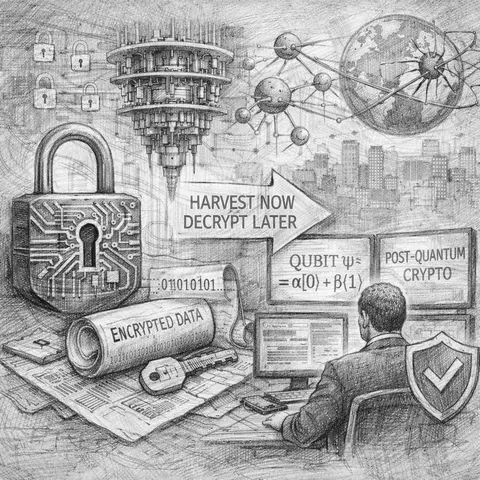
Quantum computing is turning long-term encryption into a present-day risk. This CISO playbook explains why crypto-agility is essential and how organizations can prepare for post-quantum threats today.
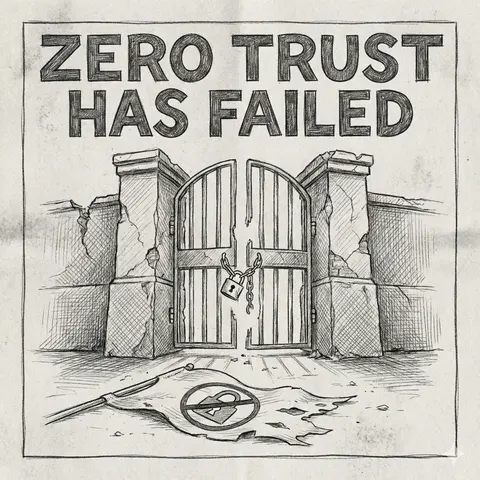
Zero Trust was supposed to eliminate implicit trust—but in practice, it often became another checkbox framework. This article examines why Zero Trust failed and how CISOs are redefining security strategies in 2026.
A practical guide for developers on maintaining application security, including dependency scanning, container CVE analysis, secure coding examples across languages, and the business importance of AppSec.
An in-depth guide to secure coding practices, explaining why they matter, common developer mistakes, and practical code examples across multiple programming languages.
A deep dive into two follow-up vulnerabilities in React Server Components — denial of service and source code exposure — how they work, their impact, and how to mitigate them.
Explains the class of vulnerabilities colloquially described as 'react2shell' (when user-controlled data from React/renderer code ends up executed by a shell), why it's dangerous, concrete vulnerable examples and safe alternatives, plus detection and mitigation checklist.
A comprehensive guide for startups to implement effective cybersecurity awareness training programs, aligned with ISO 27001 best practices, practical examples, and technical guidance.

A structured guide for assessing and comparing maturity levels across ISO/IEC 27001 security domains.
A practical guide for developers and security practitioners on secure coding principles, common vulnerabilities, prevention techniques, and real-world code examples.